Hacked data from millions of 23andMe users contains personal and genetic data. If this information is released, experts say there is no way for individuals to recover their privacy. The incident raises larger questions about privacy and genetic testing.
Since 23andMe started offering at-home genetic testing, more than 10 million people have used their service to learn more about their ancestry — and their genetic risk of developing a variety of diseases by looking for genetic variants. For example, many people use 23andMe to see whether they carry a variant of the APOE gene that confers a higher risk of developing Alzheimer’s.
Last month, a hacker posted to an online forum leaked data belonging to one million Jewish users, including names, locations, DNA profiles, and ethnicities. The hacker later deleted the original post and instead offered to sell this data to the highest bidder. In response, there are now at least four class action lawsuits against 23andMe, with users seeking relief for this privacy breach.
“As it turns out, the company’s servers were not hacked. Rather, hackers targeted hundreds of individual user accounts — allegedly those that had repeated passwords,” wrote Ignacio Cofone, an associate professor of law at McGill University, in an explainer on the event. “After gaining access to the accounts, hackers could leverage the ‘DNA relatives matches’ function of 23andMe to get information about thousands of other people.”
He and other experts agree: The event challenged the ways we think about privacy, data security and corporate accountability in the information economy.
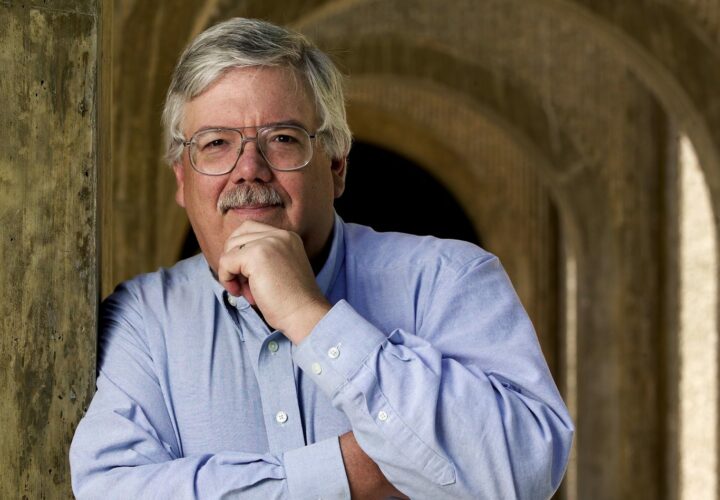
“The main problem is that this information cannot be changed,” University of California Santa Barbara computer science professor and cybersecurity expert Giovanni Vigna told Being Patient. “While you can always re-issue a credit card or change your bank account number, your genetic data is forever, and, therefore, forever compromised. Once your data is out, there is no way to recover from the loss of privacy.”
How did the data get compromised?
Many people use the same username and password (or a variation of it) across multiple websites and services like Facebook, PayPal, and shopping apps. When one of these apps is hacked, and someone obtains usernames and passwords associated with specific emails, they can try to use them to log into other services. This is called “credential stuffing,” which allowed the 23andMe hacker to obtain this data.
But this doesn’t mean that users were responsible for their own data getting leaked.
So many apps and services require users to create a unique username and password, but don’t go the extra steps to explain why that is important or enforce security practices for its users.
“Once your data is out, there is no
way to recover from the loss of privacy.”
“I think companies should be very upfront with users about the risks associated with collecting the users’ data,” Vigna said. “Security investments are really difficult to motivate because the return is incredibly hard to quantify [for companies].”
In other words, asking for forgiveness after the matter is much easier than beefing up security beforehand.
It also doesn’t help that the information collected by 23andMe and other DNA-testing companies is not currently regulated by the Health Insurance Portability and Accountability Act (HIPAA), which is the strictest health privacy law in the US.
Can you delete your data from 23andMe?
It is possible to get companies like 23andMe to delete some of the data they’ve collected about you — this is a legal requirement in some states.
Additionally, many services like 23andMe have an option within the account settings where a user can request that their information be deleted. 23andMe tells users that the company and its partner lab will hang onto your “genetic information, date of birth and sex,” after the account is deleted, per state and federal legal requirements, and while the company states that this data remains anonymous, it is still possible in some cases to re-identify the genetic data.
What if your genetic data was leaked?
23andMe is still working with third-party forensic investigators and law enforcement to determine the scope of the breach.
“If we learn that a customer’s data has been accessed without their authorization, we will notify them directly with more information,” the company said in a press release.
Once genetic information is leaked, not much can be done. “Knowing the real or potential health history of an individual might be leveraged to create bespoke scams,” Vigna warned.
According to researchers, people with mild cognitive impairment and Alzheimer’s could be more susceptible to these scams. A bad actor could target people based on their Alzheimer’s risk to take advantage.
The current regulatory shortcomings of data privacy
According to Cofone, there was a certain degree of legal blindness as to the possibility of such a risk of all this interconnected data, due to our being distracted by a fixation on data privacy as an individual issue. “As a consequence, companies can exploit one person’s agreement to legitimize data practices involving others,” he wrote. “Companies’ legal obligations to obtain individual agreements for data collection fail to recognize broader interests beyond those of the person who agreed. We need privacy laws attuned to how the information economy works. Providing consent on behalf of others, as 23andMe users did when they clicked ‘I agree,’ would be illegitimate under any meaningful notion of consent. To contain group data harms like those this hack produced, we need substantive rules about what companies can and can’t do.”
Guidance on how to improve cybersecurity
While there is no foolproof way to prevent data from getting leaked in the future, there are a few simple steps anyone can take today to secure their data.
“Knowing the real or potential health
history of an individual might be leveraged
to create bespoke scams.”
Use unique usernames and strong passwords for each app or service to ensure that if the username/password combination for your email or PayPal is leaked, it can’t be used to log into any of your other accounts. You can even use a password manager like Bitwarden or OnePass to store these credentials, so you don’t need to remember them.
Make sure to enable multi- or two-factor authorization (MFA/2-FA). When this is active, a website or app will require additional information besides the username and password to log in. Users can either have the app or service send a text message with a temporary code or use a phone app like Authy to generate special codes for login.
Ultimately, regulators may need to step in to ensure that companies are also doing their part in keeping data safe. Vigna pointed to General Data Protection Regulation (GDPR) laws, which govern companies collecting medical information in Europe more accountable to consumers.

I have absolutely NO concern about privacy of my DNA or other data–I am what/who I am and others knowing or not knowing information about me changes nothing!